- A Beginner’s Guide to Setting Up a Private LTE NetworkGet started with your own secure, reliable LTE connection. This beginner's guide to setting up a private LTE network simplifies...
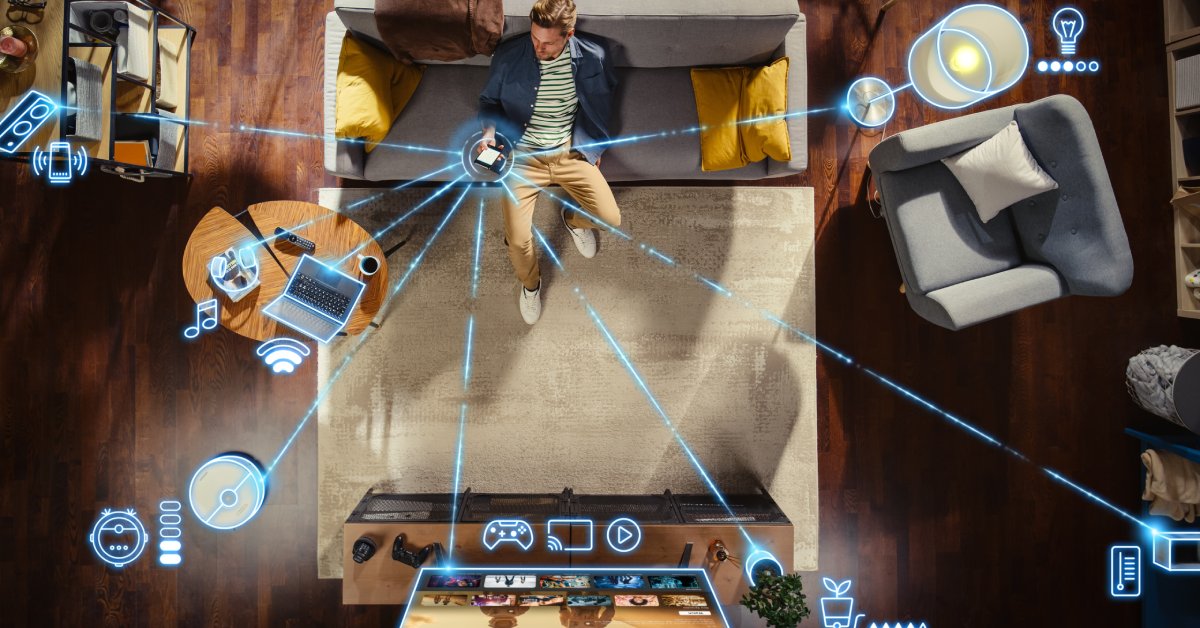
- The Intersection of Secure Phones and IoT: What To KnowSecure phones are vital for protecting IoT ecosystems from data breaches and cyber risks. Here's what to know about the...
- Top Features of Secure Cell Phones for Maximum PrivacyProtect your data with confidence. This guide covers the top features of secure cell phones for maximum privacy and shielding...
- Tips for Choosing the Most Secure Phone Service With BittiumProtect your privacy with insights and tips for choosing the most secure phone service with Bittium. Learn how to safeguard...
- How Private LTE Networks Outperform Other Wireless CarriersLet’s examine how private LTE networks outperform other wireless carriers so you can get a better idea of how to...
- How Private LTE Networks Enhance Security for Mobile UsersNavigate the Internet and perform everyday tasks with more peace of mind by learning how private LTE networks enhance security...
- Preventing Eavesdropping on Mobile DevicesUncover the information you need to start preventing eavesdropping on mobile devices. This guide covers ways you can enjoy privacy...
- 6 Tips for Navigating Mobile Security in the MetaverseReflect on each of these easy tips for navigating mobile security in the Metaverse if you want to embrace this...
- How Remote SOCs Influence Cybersecurity PracticesExpand your understanding of how remote SOCs influence cybersecurity practices and find successful ways to implement this security system into...
- The Impact of 6G on Mobile Device SecurityThe transition from 5G to 6G is more than just a technological leap—it’s an evolution that will reshape how we...