- Protecting Your Privacy While Using Public Wi-Fi NetworksProtect your data and stay secure online. This guide discusses how to protect your privacy while using public Wi-Fi networks...
- Why Corporations Are Switching to Secure PhonesCyber threats are evolving, and businesses must adapt. See why corporations are switching to secure phones to protect sensitive data...
- The Role of AI in Improving Encrypted CommunicationAI has transformed digital security. The role of AI in improving encrypted communication ensures stronger privacy and protection against evolving...
- How To Securely Store & Manage Encryption Keys on Your PhoneProtect your data by learning how to securely store and manage encryption keys on your phone. Find practical tools and...
- Guide to Understanding End-to-End Encryption on Cell PhonesUnderstanding end-to-end encryption on cell phones is key to protecting your privacy. Get clear, concise insights on secure communication methods.
- How To Transition From Regular Phones to Secure Cell PhonesProtect your data and privacy with secure cell phones. Find out how to transition from regular phones to secure ones...
- The Role of AI in Bittium’s Encrypted Communication ServicesGain insights into the role of AI in Bittium’s encrypted communication services, ensuring advanced security and efficiency for secure communication.
- A Beginner’s Guide to Setting Up a Private LTE NetworkGet started with your own secure, reliable LTE connection. This beginner's guide to setting up a private LTE network simplifies...
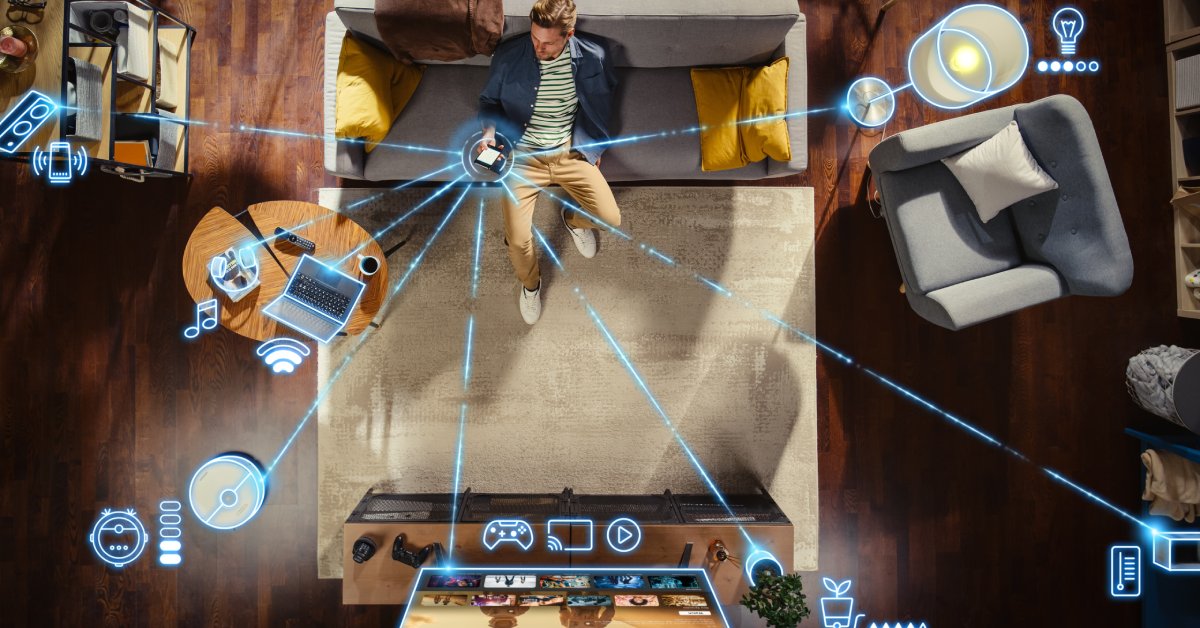
- The Intersection of Secure Phones and IoT: What To KnowSecure phones are vital for protecting IoT ecosystems from data breaches and cyber risks. Here's what to know about the...
- Top Features of Secure Cell Phones for Maximum PrivacyProtect your data with confidence. This guide covers the top features of secure cell phones for maximum privacy and shielding...